Cyber Security Awareness
for Senior Leaders
Practical guidance for protecting your organisation
– without the jargon.

The business risk
Modern cyber‑attacks are now one of the most serious risks to UK organisations. This isn’t an IT problem — it’s a business continuity issue.
Why it matters:
-

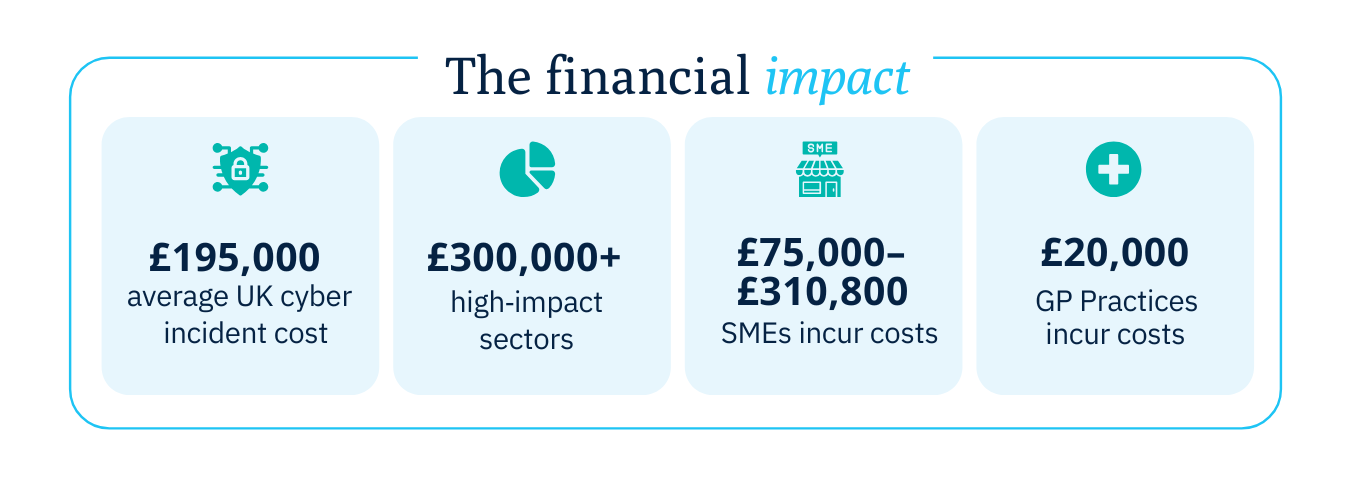
Financial loss
Fraud, recovery costs and cost revenue.
-

Operational Downtime
Business disruption and service interruption.
-

Legal Exposure
Regulatory breaches and penalties.
-

Reputational Damage
Erosion of trust and credibility.
-

Customer Churn
Loss of clients, reduced loyalty, and declining long‑term revenue.
Attacks are now routine and in a 12 month period ending in 2025:
-
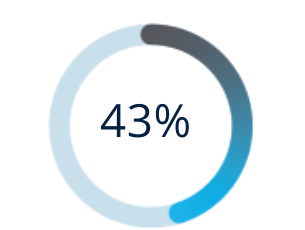
...of UK businesses suffered a breach
Source: UK Government Cyber Security Breaches Survey 2025
-
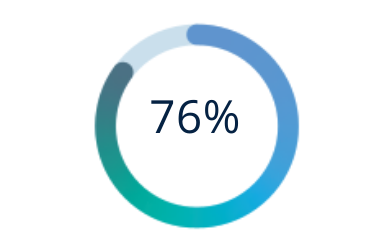
...experienced attempted attacks
Source: Cohesity Global Cyber Resilience Report 2025
-
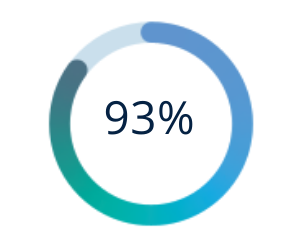
...of successful breaches began with phishing
Source: UK Government Cyber Security Breaches Survey 2025
-
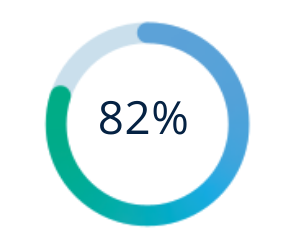
...caused by human error
Source: Verizon Data Breach Investigation Report 2024
Would your organisation survive a serious breach?
Cyber criminals increasingly target organisations because one breach gives them access to multiple systems and sensitive environments.
Leaders play a critical role in reducing that risk.
10% of UK business leaders say their organisation would be unlikely to survive a major cyber-attack.
Modern cyber-security threats…
Modern cyber threats target everyday behaviour and common technology weaknesses, making every organisation vulnerable — regardless of size, sector or technical maturity.
-
Phishing
Fake emails or messages impersonating trusted sources.
Impact: Fraud, ransomware, data theft
Likelihood: Very high
-
Malware
Malicious software designed to steal data or disrupt systems.
Impact: System outages, data loss, reputational damage
Likelihood: High
-
Weak Passwords
Simple or reused passwords easily cracked by attackers.
Impact: Unauthorised system access, data compromise
Likelihood: High
-
Out-of-Date Systems
Software missing critical security updates and patches.
Impact: Rapid exploitation of known vulnerabilities
Likelihood: Medium/High
-
Mobile & Home-Working Risks
Unsecured personal or remote devices accessing company data.
Impact: Data leakage, network compromise
Likelihood: Medium
How organisations should protect themselves…
Adds a second verification step beyond passwords, such as a code or app prompt.
Why it matters: Stops most attacks before access is gained.
Teaches employees how to spot scams and respond safely.
Why it matters: Human error causes most breaches, training reduces risk.
Ensures email, files and collaboration tools are securely configured and backed up.
Why it matters: Misconfiguration exposes the entire organisation.
Blocks access to known malicious websites and unsafe content.
Why it matters: Prevents attacks even when mistakes happen.
Continuous monitoring detects and responds to threats in real time.
Why it matters: Attacks often occur outside working hours.
Simulated attacks identify weaknesses before criminals do.
Why it matters: Fixes risk as proactively, not after a damage.
Provides real-time visibility of security posture and risks.
Why it matters: Enables informed leadership decisions quickly.
10 Practical steps for senior leaders.
These are leadership decisions, not technical tasks
— they directly reduce business risk
-
1. Cyber‑Security Policy
Sets expectations, responsibilities and controls for everyone. -
2. Compliance With Standards
Improves resilience and supports customer/contract requirements.
-
3. Incident Review
Understanding past issues helps prevent repeat attacks.
-
4. Disaster Recovery Plan
Ensures your organisation can continue operating after a breach.
-
5. Strong Passwords & 2FA
One of the simplest, most effective ways to stop attackers.
-
6. Software Updates
Fixes known vulnerabilities quickly and cheaply.
-
7. Core Protections
Anti‑virus, firewalls and monitoring form the baseline of defence.
-
8. Secure Remote & Mobile Devices
Endpoints must be protected everywhere, not just in the office.
-
9. Regular Staff Training
Human error is the biggest cause of breaches — training reduces it.
-
10. Security Audits / Pen Tests
Independent review ensures nothing is missed.
Take the first step
We’ll review your answers and provide clear, practical guidance — focused on business risk, not technical detail.
Protect your organisation, Strengthen your leadership.
Start today.